So it has been a few months since I posted anything, and even longer since I posted anything really relevant to my industry. So with a few topics I have seen over the last few weeks, I figured its time for a rant.
Topics to be covered:
1. SJWs ruining the Computer Technology Culture with PC (Politically Correct) Terminology
2. The Reason why you should use a different password for each account you have online.
SJWs are starting to ruin Comp Tech Culture with their PC Nastiness
The term SJW, or Social Justice Warrior is not new, and they have their hands in everything from politics to music… And in some cases both, I mean we just changed our National Anthem so that it was more “Gender Neutral” (read the article here). But now they are trying to attack the one last bastion I have left that has been untainted by these foul fiends… Computer Technology Terminology.
Yes, that is right… these Politically Correct Nightmare Hounds have bled their way into how we use terminology in the tech industry (read the article here). For years we have referred to the relationship between primary and secondary servers as Master and Slave, this is NOT to be confused with the bad rap these terms have been given due to slavery in the South. Master/Slave relationships in Comp Tech are more akin to Master/Slave terminology in BDSM than it does with Slavery. In the south, during times of Slavery, HUMANS were enslaved by the white man to tend their cotton crops with no compensation… The white man (read master) owned the slaves and could trade them off, or do whatever they wanted… This is indeed appalling. However, Comp Tech Master/Slave is so far from this, for one, they are inanimate mechanical objects with no rights, souls or minds of their own (yet). Secondly, the relationship is not one of abusive nature nor does the master own the slave, in fact, the relationship is technically consensual. The relationship in most cases is directional, the master holding the original content, the slaves holding backups. In many cases, the master also holds the configurations for all the servers in the cluster.
So why are the SJWs so butthurt? Why do they have to change everything so that the minority of people who are offended (read snowflakes) can be happy? I mean I am still having issues with the change to files sizes… Yes that’s right, there was a change to that years ago… A Megabyte, which used to be 1024KB is now a Mebibyte (read this article). Now we have the SJWs wanting to change every word they find offensive because of unrelated events. Stick to the politics, stick to music, just whatever you do, get you damn filthy SJW paws off Comp Tech, it’s the only place I feel safe from you bastards. Next thing you know you’re gonna wanna “Gender Neutralize” cables, as currently there is a female and male counterpart to cables.
Why should you use a different password for each site online?
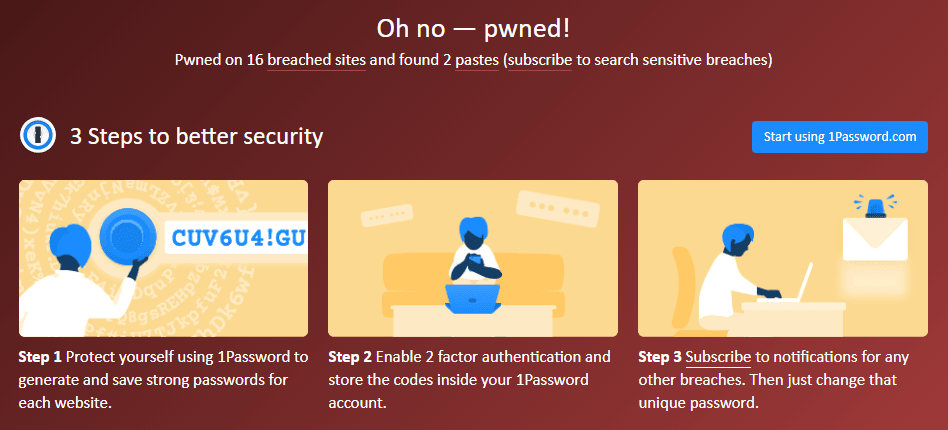
This part of the rant is less “F*ck the World” and more “YOU HAVE BEEN WARNED”. A recent article was published about the data breach of NCIX (read the article here) which shows just how easy it is for your personal data to be leaked. A quick way to find out if your info has been leaked in the past is a site called Have I been Pwned which will tell you how many breaches your email has been discovered in.
Ever get an email from a site or service you use that says a request for a password reset has been created? Chances are you were in a breach… I personally have had my Origins (EA) account as well as a few other services hacked into because of this. And because I normally use the same password, pretty much any service I used was put at risk.
Ever since then I have started to use a different password for all major services that contain personal information. There are two ways you can do this. One is to use a derivative password… by this I mean its something easy to remember, but changes slightly based on the website. The other is to use a password manager, I use KeePass, which is an application I have on my phone and desktop. “But why not use one of those online based Password managers?”… Well, seeing as the topic here is online breaches… and the online password managers are ONLINE… whats to say they won’t be the next target or a breach? No thanks, I keep my encrypted password database stored in the cloud, however, but that is as far as I will go… the key and password to unencrypted are stored locally, so even if the cloud server is breached, it is highly unlikely they will be able to crack the database.
Personally, I use a mixture of both. For my servers, I use KeePass with randomly generated 32 to 64 character passwords that I change every 6 months. For the more day-to-day sites, I use a derivative that I can easily remember (at least within the first 2 or 3 tries). I know it’s a pain in the butt, but in the end with the rapid advancement of technology and the slow pace at which security protocols advance in comparison (I mean there is no excuse for a site this day and age to be storing plain text passwords) if you are using one password everywhere, you are putting yourself at risk… if you use one password per site, if that site gets breached, you need only change one password… not 2-100+passwords (depending on how active you are on the net) and it will also limit the amount of data that is compromised.
Now as for the Credit card information, well… that’s a topic for another rant…